Authorization and management of personal data
W1hen passing by the url address where the terminal is located, an unauthorized user sees the authorization form.
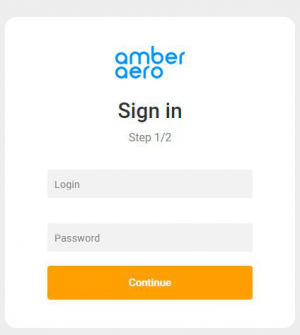
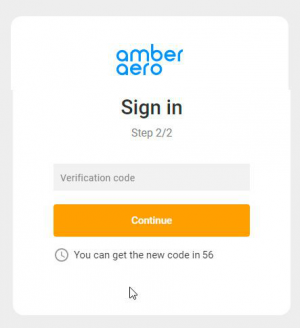
The terminal uses a two-factor authorization, so the procedure itself takes place in two stages.
On the first - user must enter his login and password in the corresponding fields.
The second step is to confirm authorization with a special code, which will be sent to the user's e-mail.
- User fills in authorization parameters - enters login and password.
- The terminal sends a request to verify the authorization data to the host.
- If the verification is successful, the following steps are executed.
- The terminal generates a verification code (lifetime 5 min).
- The terminal generates and sends an email containing the code to the email address associated with the user's account.
- The terminal displays the form for entering the code to the user.
- You can resend the code (steps 1 and 2 will repeat).
- User enters the code.
- The terminal checks the entered and generated code for coincidence.
If the check is successful, the user is authorized.
After authorization user enters his personal account page with main sections:
- Start page.
- Search for a new flight.
- Search of the previously created order.
- A section for working with queues.
- The list of queues with the counter of events waiting to be processed.
- And the list of events of each queue for processing.
- Account data.
- You can view the personal data of the account ONLY.
- Password change.
- Signing out from an account.
Personal account information
User data is returned in response to successful authorization. Set of parameters available:
- First name
- Last name
- Phone
Password change dialog
- User requests to change a password.
- Terminal displays form for changing password.
- User enters old and new password, repeats new password.
- The terminal sends a request for data verification (login and old password) to Amber.
- If the verification is successful, the following steps are performed. If the verification reveals an error in the entered data - the user will see a corresponding validation message.
- The terminal generates a verification code (lifetime 5 min).
- The terminal generates and sends an email with the code to the email linked to the user's account.
- The terminal shows the user the form for entering the code.
- The code can be resent.
- The user enters the code.
- The terminal checks if the entered code matches the generated code.
- If the check is successful, the following steps are performed.
- Terminal sends a request to Amber to save a new password.
- Sends a notification of password change to the user's email address.
Password recovery
You can recover your password by contacting the Amber support team. A techsupport employee changes the password and sends it to the cashier operator via email.